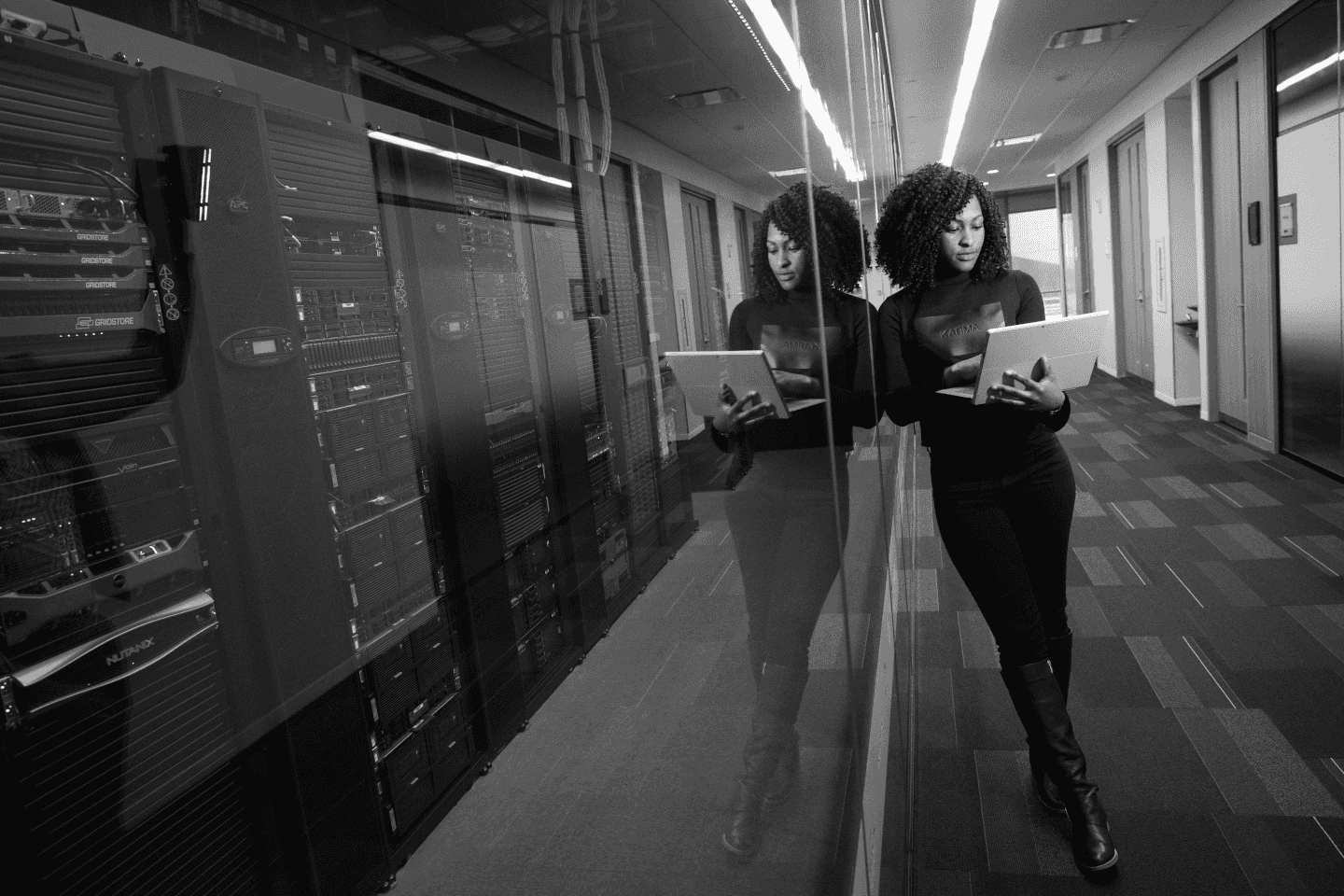
A Comprehensive Approach to Security, Compliance and Risk Management
Cloud-Dog Solutions provides innovative solutions designed to address complex business challenges. We help you transform operations and drive sustainable growth through strategic implementation.
Risk Mitigation
Identify and address potential risks before they impact your business operations and growth.
Data-Driven Insights
Leverage advanced analytics to make informed decisions and optimize business performance.
Seamless Integration
Integrate solutions smoothly with your existing systems and workflows for maximum efficiency.
Our Solution Methodology
We follow a proven, four-phase methodology to ensure successful solution delivery, customized to your unique business requirements.
Assessment
We conduct a comprehensive analysis of your current situation and identify key opportunities.
Strategy
Our team develops a customized solution strategy aligned with your business objectives and requirements.
Implementation
We deploy the solution systematically with thorough testing and quality assurance processes.
Optimization
Ongoing monitoring and refinement ensure maximum value and continuous improvement.
Explore Our Solutions
Discover more ways we can help transform your business
Our security, compliance and risk management services provide an end-to-end approach to protecting your information, platforms and services across cloud, hybrid and on-premise environments.
We help you define security policies, standards and controls aligned to your risk appetite and obligations (including ISO27001, NIST, CIS, Cyber Essentials, DPA/GDPR and sector regulations). We design and implement security architectures and controls across identity and access management, network security, encryption, endpoint protection, data loss prevention, vulnerability management and incident response.
Using Cloud Security Design and Compliance as Code patterns, we automate compliance and technical controls wherever possible – embedding checks and guardrails into Infrastructure as Code, DevSecOps pipelines and platform engineering. This includes continuous configuration and patch management, automated hardening, and real-time monitoring and alerting across SIEM, logging, auditing, firewall/WAF, content proxy and content inspection capabilities.
We work with your teams to establish practical security operations and governance: risk registers and treatment plans, KPIs and KRIs, playbooks, incident management, and integration with SOC and wider operational processes. Our consultants can augment your own security, architecture and engineering teams or lead specific work-streams.
The result is a stronger, more transparent security posture – with cloud and traditional services that are properly configured, monitored and tested, reduced likelihood and impact of cyber incidents, and clearer evidence of compliance for regulators, auditors and senior stakeholders.